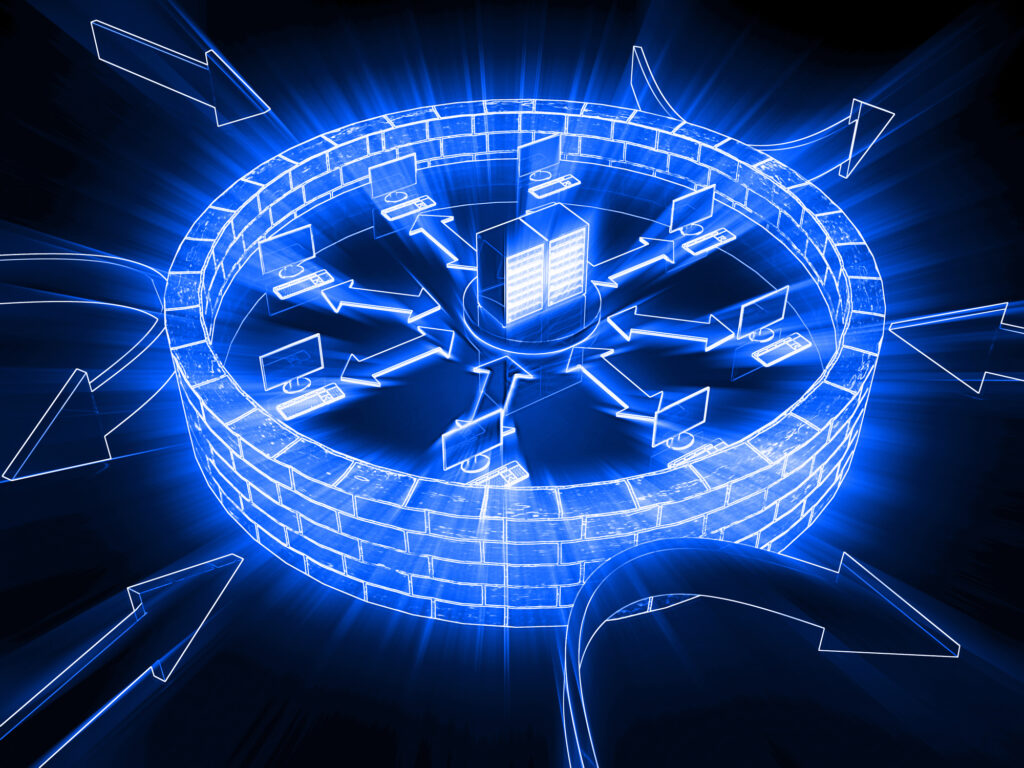
In the intricate web of network security, the cornerstone of cyber defense lies in the venerable firewall. This blog on firewall configurations will unravel the complexities, pinpointing the essential items that are the mainstay of your network’s security, especially in the face of malware and advanced threats.
Harnessing Firewall Power: Essential Types and Configurations
Each firewall type serves as a unique champion in defending your digital domain against malicious traffic, unauthorized access, and various cyber threats. Let’s scrutinize these cyber sentinels more closely, including both software and hardware firewalls.
The Sentinels of the Cyber Realm
Packet Filtering Firewall: These gatekeepers scrutinize every data packet—source IP addresses, destination ports (including TCP/UDP port numbers), and more—to ensure only legitimate network traffic gains admittance. They operate at the network layer of the OSI model, providing a basic, yet formidable, defense.
Stateful Inspection Firewalls: Elevating the game, these firewalls not only inspect packets but also memorize the status of ongoing connections, such as the TCP handshake process, making them aware of the context of the traffic for more secure screening.
Proxy Firewalls (Application-level and Circuit-level Gateways): Acting as intermediaries, these firewalls, including proxy servers, filter traffic at the application layer, preventing direct interactions and enhancing control and anonymity.
Cloud-based and Next-generation Firewalls (NGFW): Armed with deep packet inspection, intrusion prevention, and application-level scrutiny, these firewalls defend against sophisticated attacks, integrating seamlessly with cloud computing environments.
NAT Firewalls (Network Address Translation): By disguising the IP addresses of devices within your private network, NAT firewalls complicate the efforts of attackers trying to pinpoint individual devices, enhancing privacy and security.
Software and Hardware Firewalls: Software-based solutions offer flexibility and are often integrated with antivirus programs, while hardware firewalls, typically embedded in routers, provide a robust barrier at the perimeter of your network.
Crafting the Shield: Firewall Rules and Policies
Configuring firewall rules and policies is akin to laying down the laws that govern your digital territory, including technologies such as access control lists (ACLs) that specify allowed and blocked traffic based on specific criteria. The correct implementation of firewall policies and port configurations is crucial for maintaining security and network performance.
When configuring your firewall, bear in mind the Tufin Orchestration Suite, a tool that simplifies the orchestration of intricate security policies. It’s your steadfast companion in firewall configuration analysis and firewall risk analysis, keeping you in line with industry benchmarks such as firewall PCI DSS compliance.
Conclusion
Understanding the diverse types of firewalls and their configurations equips you to select the most robust protection for your network. The ideal arrangement often involves a blend of different firewall types, alongside other security solutions like antivirus and VPNs, ensuring comprehensive defense against external threats and unauthorized access.
FAQs on Firewall Configurations
Q: What are the different types of firewall configurations and how do they function in networking?
A: From packet filtering to next-generation firewalls, each type plays a vital role in network security, handling everything from basic access control to advanced threat prevention. Firewalls work by examining network traffic and making decisions based on predefined rules, ensuring the security of computer networks.
Q: Can you explain the primary firewall architecture types and the significance of firewall rules in securing a network?
A: The principal firewall architectures—packet-filtering, stateful inspection, proxy (circuit-level and application-level), and next-generation—serve various functions, from filtering based on set rules to advanced inspection of connection states and packet contents. Firewall rules are critical for allowing or blocking traffic, ensuring that only legitimate traffic passes through.
Q: How do firewall policies and port configurations affect the security and functionality of a business network?
A: Firewall policies define the security boundaries, while port configurations determine the traffic’s entry and exit points. Proper management of these elements is crucial for protecting against external threats and ensuring operational efficiency.
Wrapping Up
For a deeper understanding, explore our posts on firewall security standards and firewall design principles. And for hands-on experience, consider a Tufin demo.
With the right tools and knowledge, your network can stand as an impregnable fortress in the ever-evolving landscape of cyber threats.
Ready to Learn More
Get a Demo