AI Is Changing Network Security. Tufin Is Leading the Way.
Learn MorePosts by Avigdor Book

Cybersecurity
Managing Access Request Spikes in Network Traffic: How Tufin Helps Ensure Security & Efficiency

Cybersecurity
Scaling Security Policy Management: Tufin’s Unmatched Approach

Firewall Best Practices
Securing the Modern Hybrid Network: Security Policy Automation

Cloud Security
Understanding Cloud Workload Security: Navigating Your Digital Transformation

Cybersecurity
Understanding Operational Technology (OT) Cyber Security
Cybersecurity
Navigating the Terrain of OT Risk Management

Cybersecurity
Active Directory Provisioning: Unveiling the What, How, and Why

Firewall Best Practices
Firewall Troubleshooting Scenarios: Unraveling Common Issues and Solutions
Cybersecurity
Understanding the Zero Trust Firewall

Cybersecurity
How End-to-End Network Visibility Improves Your Hard-to-Assess Security Posture

Network Security Automation
How Automated Cloud Security Tools Support Audit Readiness

Cybersecurity
Understanding the Role and Value of a DMZ Environment

Cybersecurity
Understanding the Shared Responsibility Model for Cloud Security
Cybersecurity
Building an Effective SOC Playbook
Cybersecurity
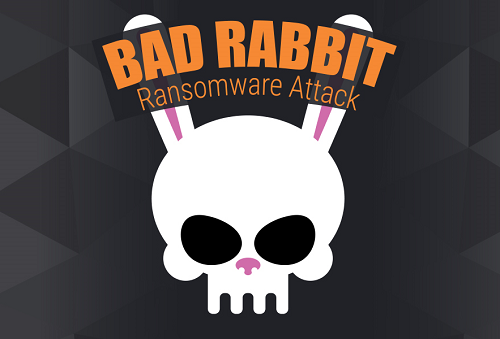
Addressing Bad Rabbit Ransomware With Tufin

Cybersecurity
Tech How-To: Configure Your Firewalls to Block the “WannaCry” Ransomware Attack

Firewall Best Practices
9 Best Practices for Optimizing Firewall Performance

Firewall Best Practices
