Many of our customers are currently using VMware NSX-V for network virtualization and are looking to migrate to VMware NSX-T™. It’s no secret that VMWare NSX-T™ is now VMware’s primary SDN solution with noted advantages, including extensive cloud-native apps support and enhanced network security features.
Tufin is the first network security policy management vendor to support VMware NSX-T, providing unified visibility and control for NSX-T and across your hybrid environment, and ensuring a smooth and secure migration path from NSX-v to NSX-T.
Tufin NSX-T support will be available in Tufin Orchestration Suite 19-3 in December 2019 for our early adopters and will be generally available (GA) in January 2020.
Manage and Secure NSX-T and Non-NSX-T in Unison
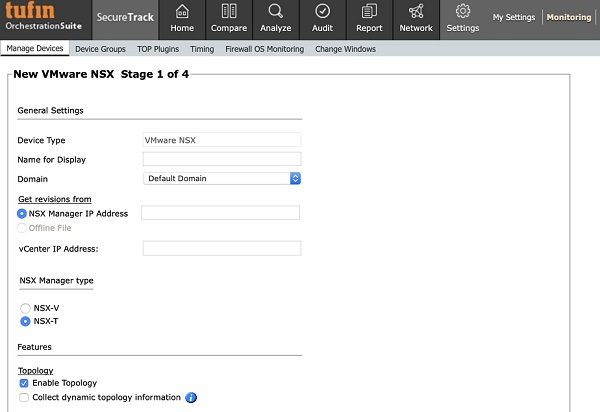
With 19-3 release Tufin users can start managing their NSX-T network security policies directly from Tufin SecureTrack . Adding NSX to SecureTrack is fast and easy. You simply go to SecureTrack ‘Monitoring’ and select ‘VMware NSX-T’ as additional environment to monitor.
How can I maintain centralized visibility into the NSX-T and beyond?
It’s essential to have accurate visibility into which apps are running and their dependencies, real-time traffic flows, and access rules. But even more important, is to have a single view of the entire network so you can apply end-to-end consistent and effective segmentation and achieve faster resolution of security and connectivity incidents.
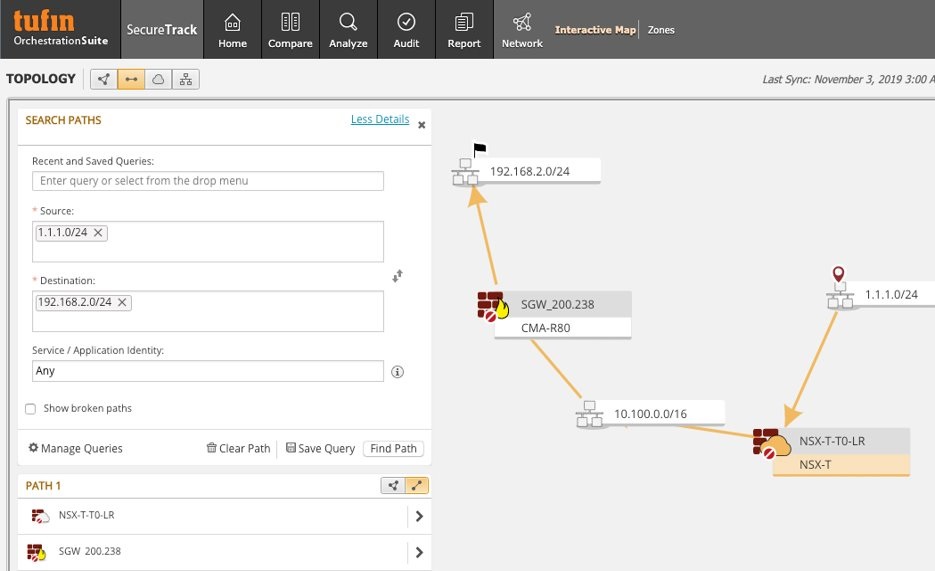
Tufin topology map gives you a greater understanding of NSX-T in relation to the entire IT environment, how traffic traverses, and the vast amount of network objects (e.g. BGP, FWs, switches, routers, etc.) across the various routes. You’ll be able to automatically detect and troubleshoot broken connectivity or misconfigured rules using Tufin’s path analysis.
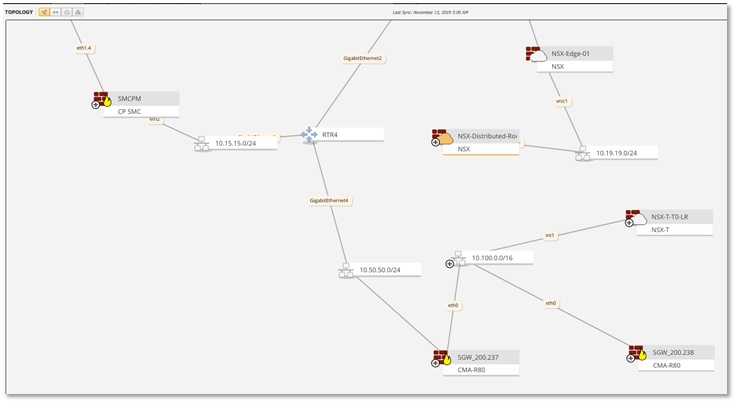
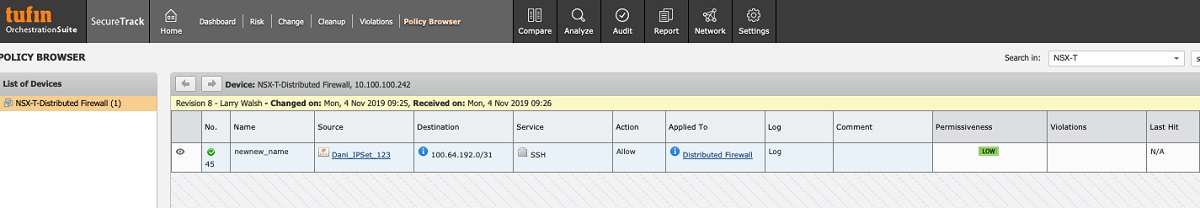
In addition, Tufin immediately starts documenting any changes made to rules. So not only do you have an accurate, full view of the environment, you can monitor rules revisions in real time for continuous compliance and audit purposes (e.g. if a rule was deleted from the policy).
How can I avoid NSX-T rule proliferation? Does the policy include only the necessary rules to allow secure traffic?
As a security best practice, it’s recommended to avoid rule cluttering which can create security risks.
Tufin can help eliminate redundant rules and recommend modifications to over-permissive rules in your NSX-v and NSX-T environments (a useful step to consider before migrating to NSX-T).
You can also search through NSX for shadowed, redundant, outdated, and overly permissive rules to prevent unnecessary access to resources, which can easily be used intentionally or unintendedly, and create a security threat.
Tufin provides meta-data for each rule, for example, the last time a rule was modified, if it’s fully/partially shadowed, rule owners, etc., to help you make an educated decision when the time comes to re-certify or decommission the rule. If needed, you can open a ticket and assign it to the rule’s owners, asking to re-certify the rule.
How can I create effective micro-segmentation for NSX-T and across the entire environment?
Network segmentation policy should be applied and enforced consistently, irrespective of the underlying platform or network objects used. This ensures that the policy is enforced for apps/workloads, regardless of where they run.
With Tufin, the same zone-to-zone matrix defining a unified segmentation policy that was applied to NSX-v, will also be applied to the NSX-T environment. In addition, you’ll gain visibility into both environments, and to the traversing traffic, while maintaining business continuity and compliance.
If you’re new to Tufin, once your environment is mapped, you can divide the topology map of the monitored network objects and apps into zones and define the relationships (rules) between the zones. The end result is a Unified Security Policy (USP) matrix that can be enforced across vendors and platforms. Tufin continuously syncs the zones, so that the matrix always represents the latest status of your network.
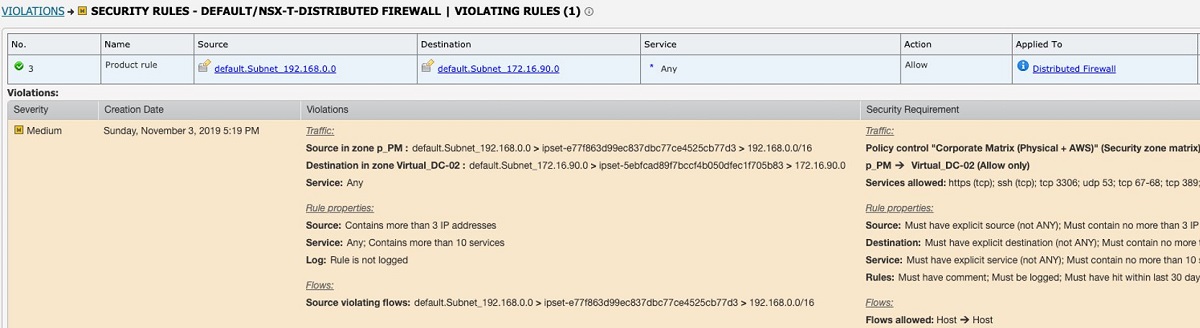
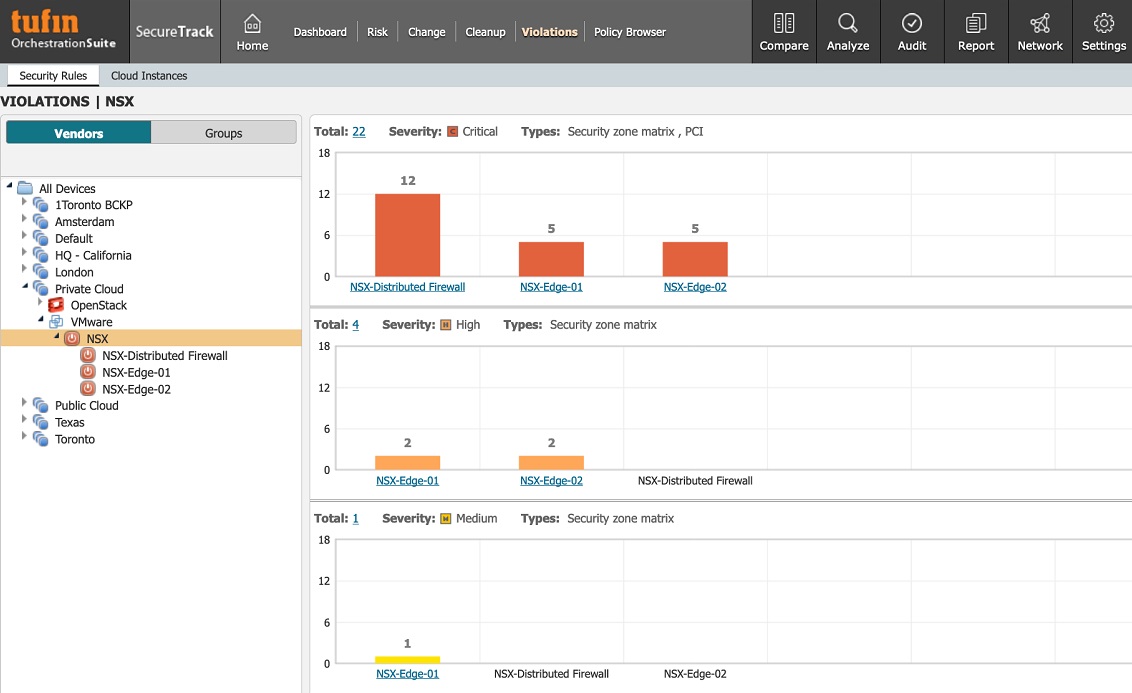
Once the USP is defined, Tufin automatically sends an alert as to which rule violates the policy and where (e.g. NSX-EDG), as well as prioritizing the criticality of the violation. We’ve invested efforts and resources to become the most accurate and reliable solution on the market today, and significantly reduce, if not fully eliminate, false-positive alerts. We also provide exceptionally granular information, so that you can view your current defined policy vs. the violations. What’s more, you can generate a violation report as needed.
How can I accelerate network access change implementation?
The process of optimizing policies and managing changes can be time-consuming and involve multiple teams. We often hear it takes days, if not weeks or more, and can result in app downtime, delays in SLAs and deployment of new services.
Tufin automates the change process by using customized workflows to reduce change implementation time to just minutes. These workflows can also be integrated with your ITSM system. Once a change request is submitted, Tufin automatically calculates risk analysis and an access path throughout the network, simulates the path and highlights which FWs and other network objects cross the selected route, and what needs to be changed to allow the requested access. You can validate the change before enforcing it. Finally, Tufin verifies that the change was successfully implemented.
Comprehensive support for VMware NSX-T is part of Tufin’s commitment to being the leading vendor managing security policies across the SDN and the rest of the hybrid network. Organizations migrating to VMware NSX-T, or adopting NSX-T, will need a central console to consistently manage security, compliance and connectivity across NSX-T and the rest of the hybrid environment. To learn more about how Tufin enhances SDN support, contact us.
Ready to Learn More
Get a Demo