Firewall Change Automation
Automate compliance and firewall audit readiness to avoid audit fines, late penalties, and other costly ramifications.
Add code-free integrations with your existing tech stack using Tufin Extensions.
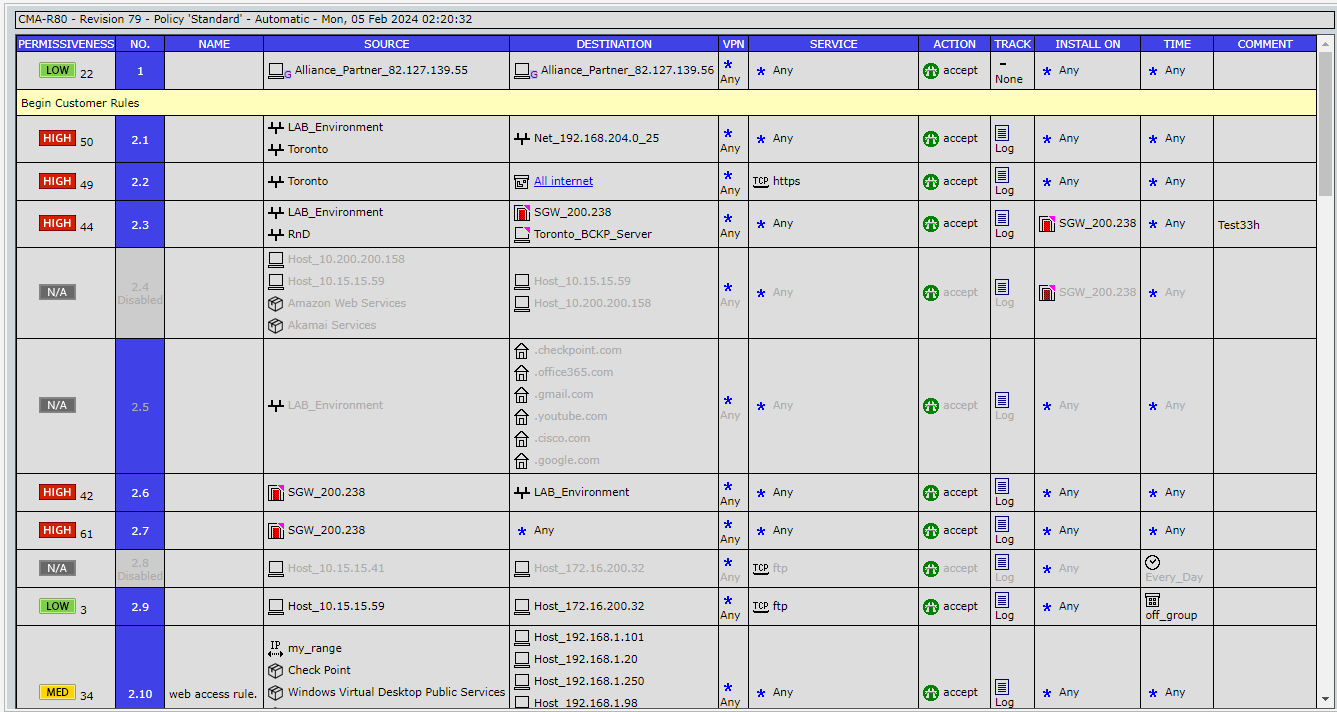
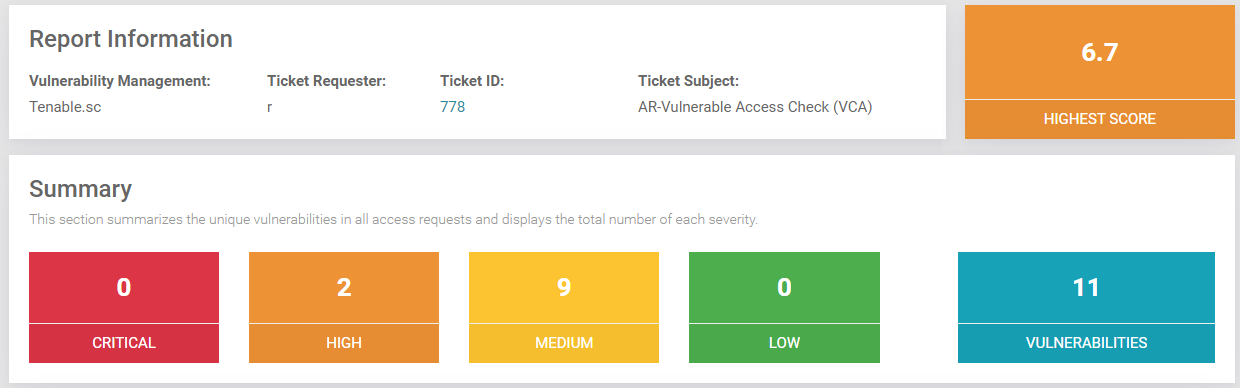
- Reduce your attack surface by running proactive analysis before you make any changes.
- Automatically create least-privilege firewall access rules, identify security risks in real time, and enforce continuous compliance.
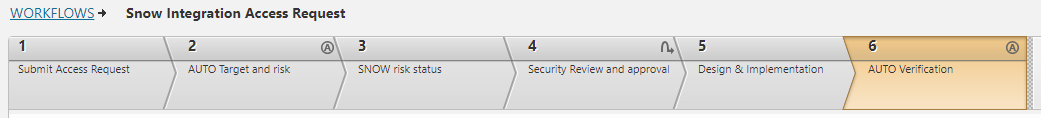
- Automate network access changes from request to implementation.
- Add code-free integrations with your existing tech stack using Tufin Extensions.
Firewall Audit Use Cases
Make Network Changes Effectively – and Easily
Leverage automated documentation of change management processes to ensure continuous compliance and minimize security issues, failed audits, and costly fines.
- Leverage a central console for monitoring, maintaining, and proving continuous compliance across firewalls and routers, SDN, and hybrid networks.
- Run ad hoc audits on infrastructure and existing firewall rules to proactively uncover violations and exceptions before they cause security issues, failed audits, and costly fines and penalties.
- Utilize built-in, pre-flight compliance checks during network changes to minimize failed audits.
- Easily create and optimize network access rules based on real network traffic analysis.
- Reduce network change SLAs by up to 90%.
Prove Audit Readiness on Demand
Demonstrate that actions have been quickly taken to meet compliance via on-demand, real-time reports.
- Provide immediate verification of firewall compliance with automated reports for internal policies, industry standards like NIST 800-53, and regulatory mandates such as PCI DSS, HIPAA, and more.
- Track and report on on-the-fly changes, approvals, and exceptions and immediately see the impact on regulatory compliance.
- Reduce report and audit trail generation from days or hours to minutes.
Accelerate Audit Preparation with Automation
Reduce preparation time from weeks to days with automated processes and audit trails for all your firewalls, internal network devices, and cloud resources.
- Gain up to a 95% improvement in efficiency for audit preparation, responses, and reporting.
- Eliminate up to a full-time equivalent of a security staff person with accelerated and automated data gathering of information.
- Maintain a history and fully documented change automation process for auditor reviews.
Get Started with Tufin
Contact our experts to learn more about pricing, receive a free network and firewall risk assessment, or schedule a demo.
Change Automation Resources
Articles
- What Is SD-WAN as a Service? Guide for Enterprise IT
- Top SD-WAN Providers and How to Compare Them
- Tufin Expands Automated Security Policy Controls to Huawei and Versa Networks
- TufinOS Launches on AWS Marketplace: Unified Platform Simplifies Network Visibility, Control, and Automation
- Simplifying IT Change Management With Predictive Insights
Solutions
Transforming Network Security & Automation
Elevate your network security and cloud security operations with Tufin’s product tiers. Addressing the most challenging use cases, from segmentation insights to enterprise-wide orchestration and automation, experience a holistic approach to network security policy management.
SecureTrack+
Firewall & Security Policy Management
Drive your security policy journey with SecureTrack+
- Centralize network security policy management, risk mitigation and compliance monitoring across firewalls, NGFWs, routers, switches, SDN and hybrid cloud
- Automate policy optimization
- Prioritize and mitigate vulnerabilities
SecureChange+
Network Security Change Automation
Enhance your visibility and automate mundane tasks with SecureChange+
- Achieve continuous compliance
- Reduce network change SLAs by up to 90% with network change design and rule lifecycle management
- Identify risky attack vectors and detect lateral movement
- Troubleshoot connectivity issues across the hybrid cloud
Enterprise
Zero-Trust Network Security at Scale
Fortify your network security operations with Enterprise
- Achieve zero-touch automation through provisioning of network access changes
- Deploy apps faster through application connectivity management
- Minimize downtime and data loss with High Availability and built-in redundancy
