混合环境的自动化网络安全
适用于大型混合环境的企业级可视性、合规性、自动化和云安全性。
了解為什麼 Tufin 得到了成千上萬名客戶的信任



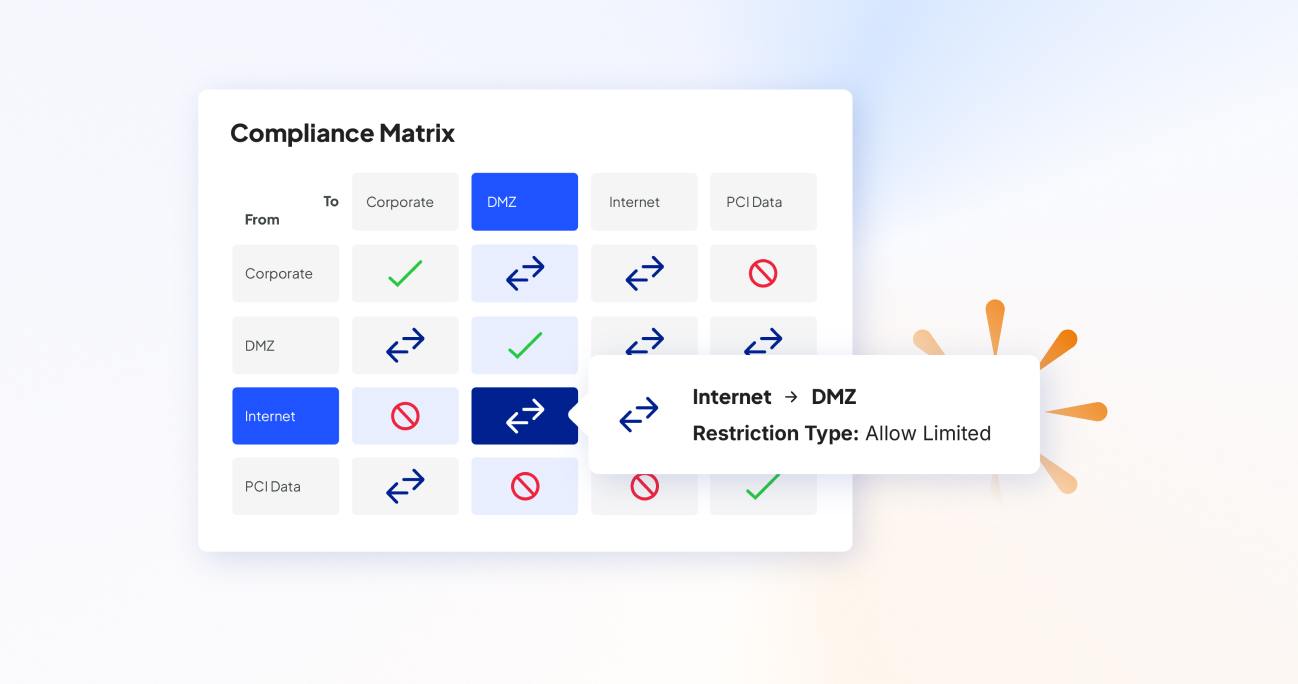
跨混合网络的可靠合规性
提高可见度。 自动化变更。 确保合规。 实现内心的平静。
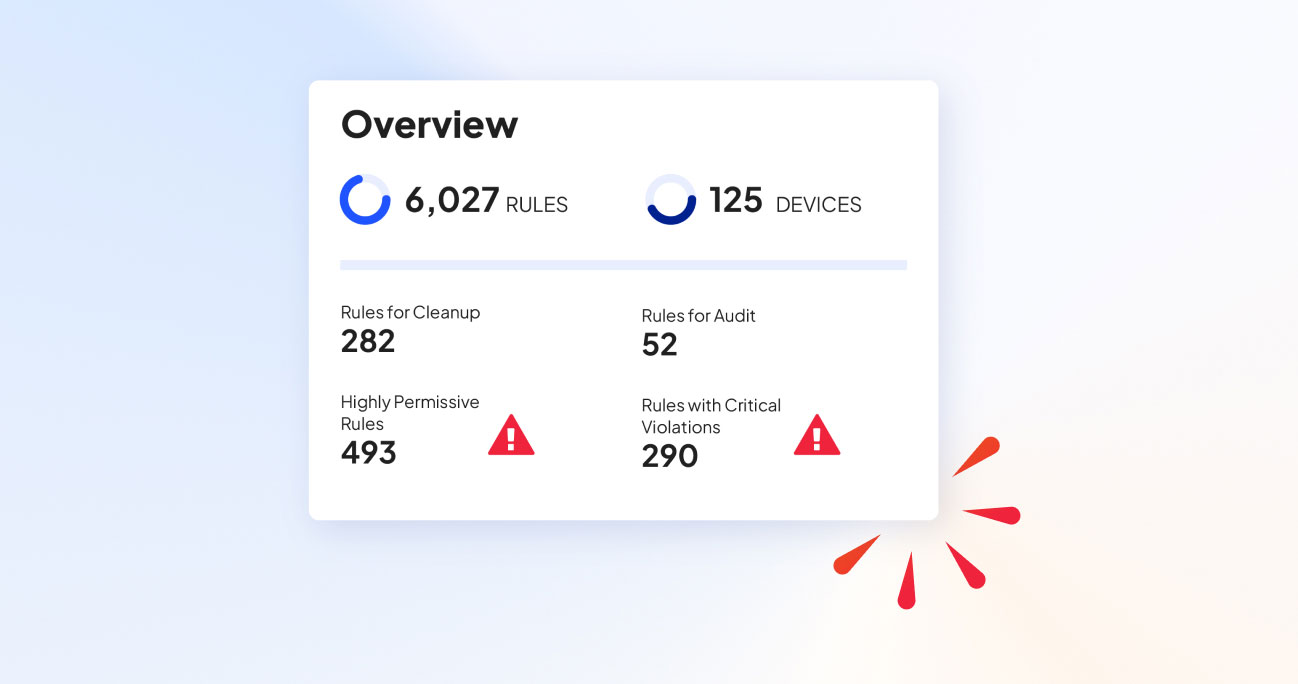
預防重大問題
全面了解您的防火牆策略,以便在潛在違規行為升級之前主動識別並解決它們。Tufin 的持續監控和警報系統可確保您的策略始終執行且安全。
增強可見性和自動化
建立一個彈性策略框架,並在整個網路中自動執行。Tufin 確保防火牆策略應用的一致性,減少人為錯誤,即使在網路變更或中斷期間也能保持安全。
充滿信心地解決
使用自動化工具無縫調整您的防火牆策略,與不斷發展的網路保持同步。無論是擴大規模、遷移到雲端,還是適應監管變化,Tufin 的解決方案都提供了適應的靈活性,同時保持強大的安全性和合規性。
網路安全綜合解決方案
我們的解決方案以強大的防火牆和雲端策略管理為基礎,增強您的網路安全性,確保合規性,自動化任務並保護混合環境。
取得 Tufin,看得更清楚。
安排您的個人化簡報
減少 SLA 時間。增加敏捷性。
無論您是管理防火牆策略、自動化任務或保護雲端環境,Tufin 都能提供適合您特定需求的解決方案。
SecureTrack+
防火牆和安全策略管理
使用 SecureTrack+ 推動您的安全策略之旅
- 跨防火牆、NGFW、路由器、交換器、SDN 和混合雲的集中式網路安全策略管理、風險緩解和合規性監控
- 自動化策略優化
- 確定漏洞的優先順序並減少漏洞
SecureChange+
網路安全
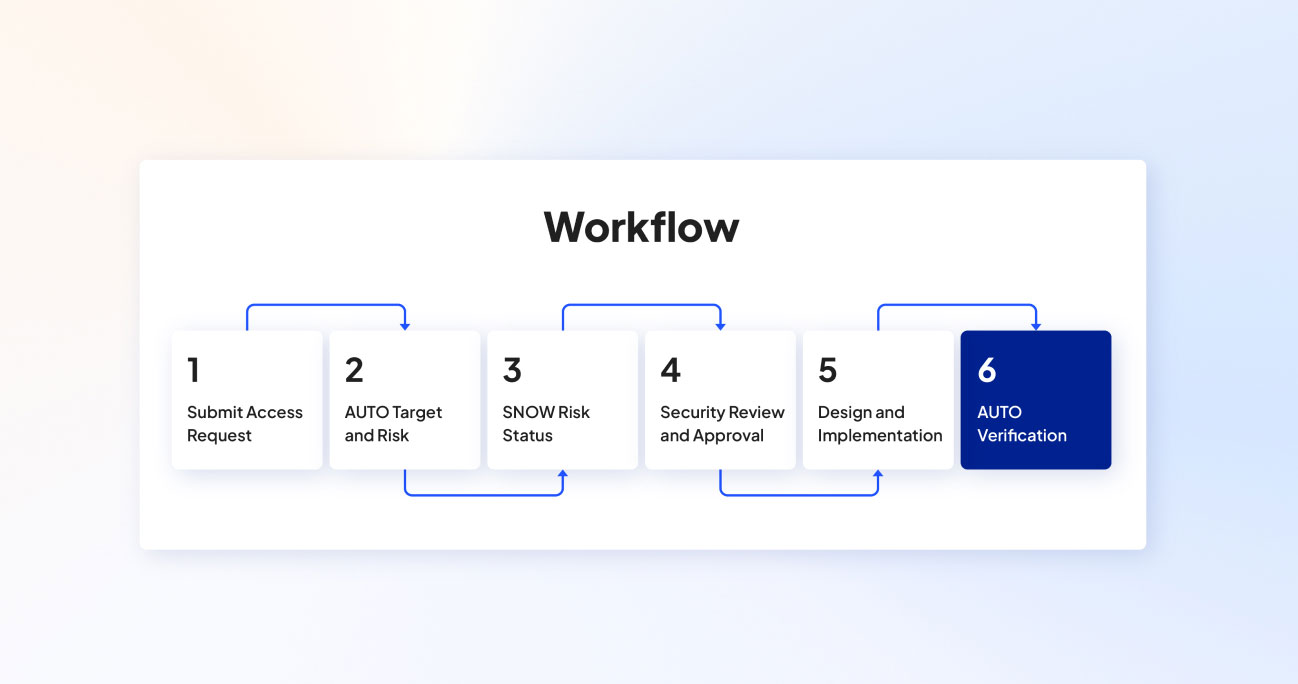
使用 SecureChange+ 增強您的可見性並自動執行日常任務
- 實現持續合規
- 透過網路變更設計和規則生命週期管理,將網路變更 SLA 減少高達 90%
- 識別有風險的攻擊向量並偵測橫向移動
- 解決混合雲中的連線問題
Enterprise
大規模零信任網路安全
通過Enterprise 強化您的網路安全運營
- 通過配置網路存取變更實現零接觸自動化
- 通過應用程式連接管理更快部署應用程式
- 通過高可用性和內建冗餘最大程度地減少停機時間和資料遺失
案例研究
使用 Tufin 獲得真實結果
了解 Tufin 的解決方案如何協助 IT 專業人員簡化營運並增強安全性。
Built for Your Responsibilities
Discover how Tufin integrates with the demands of your work.
Centralized Visibility
- Monitor and manage all firewall policies from a single interface with SecureTrack.
- Quickly identify and address potential security threats across the network.
Consistent Policy Enforcement
- Ensure uniform application of security policies across multiple firewalls, reducing the risk of unauthorized access.
Automated Policy Updates
- Use SecureChange to automate routine policy updates, minimizing manual errors and freeing up time for critical tasks.
Centralized Visibility
- Monitor and manage all firewall policies from a single interface with SecureTrack.
- Quickly identify and address potential security threats across the network.
Consistent Policy Enforcement
- Ensure uniform application of security policies across multiple firewalls, reducing the risk of unauthorized access.
Automated Policy Updates
- Use SecureChange to automate routine policy updates, minimizing manual errors and freeing up time for critical tasks.
Centralized Visibility
- Monitor and manage all firewall policies from a single interface with SecureTrack.
- Quickly identify and address potential security threats across the network.
Consistent Policy Enforcement
- Ensure uniform application of security policies across multiple firewalls, reducing the risk of unauthorized access.
Automated Policy Updates
- Use SecureChange to automate routine policy updates, minimizing manual errors and freeing up time for critical tasks.
Centralized Visibility
- Monitor and manage all firewall policies from a single interface with SecureTrack.
- Quickly identify and address potential security threats across the network.
Consistent Policy Enforcement
- Ensure uniform application of security policies across multiple firewalls, reducing the risk of unauthorized access.
Automated Policy Updates
- Use SecureChange to automate routine policy updates, minimizing manual errors and freeing up time for critical tasks.
Centralized Visibility
- Monitor and manage all firewall policies from a single interface with SecureTrack.
- Quickly identify and address potential security threats across the network.
Consistent Policy Enforcement
- Ensure uniform application of security policies across multiple firewalls, reducing the risk of unauthorized access.
Automated Policy Updates
- Use SecureChange to automate routine policy updates, minimizing manual errors and freeing up time for critical tasks.
Centralized Visibility
- Monitor and manage all firewall policies from a single interface with SecureTrack.
- Quickly identify and address potential security threats across the network.
Consistent Policy Enforcement
- Ensure uniform application of security policies across multiple firewalls, reducing the risk of unauthorized access.
Automated Policy Updates
- Use SecureChange to automate routine policy updates, minimizing manual errors and freeing up time for critical tasks.
Centralized Visibility
- Monitor and manage all firewall policies from a single interface with SecureTrack.
- Quickly identify and address potential security threats across the network.
Consistent Policy Enforcement
- Ensure uniform application of security policies across multiple firewalls, reducing the risk of unauthorized access.
Automated Policy Updates
- Use SecureChange to automate routine policy updates, minimizing manual errors and freeing up time for critical tasks.
Centralized Visibility
- Monitor and manage all firewall policies from a single interface with SecureTrack.
- Quickly identify and address potential security threats across the network.
Consistent Policy Enforcement
- Ensure uniform application of security policies across multiple firewalls, reducing the risk of unauthorized access.
Automated Policy Updates
- Use SecureChange to automate routine policy updates, minimizing manual errors and freeing up time for critical tasks.
Firewall Administrators
Centralized Visibility
- Monitor and manage all firewall policies from a single interface with SecureTrack.
- Quickly identify and address potential security threats across the network.
Consistent Policy Enforcement
- Ensure uniform application of security policies across multiple firewalls, reducing the risk of unauthorized access.
Automated Policy Updates
- Use SecureChange to automate routine policy updates, minimizing manual errors and freeing up time for critical tasks.
Network Security Analyst
Centralized Visibility
- Monitor and manage all firewall policies from a single interface with SecureTrack.
- Quickly identify and address potential security threats across the network.
Consistent Policy Enforcement
- Ensure uniform application of security policies across multiple firewalls, reducing the risk of unauthorized access.
Automated Policy Updates
- Use SecureChange to automate routine policy updates, minimizing manual errors and freeing up time for critical tasks.
IT Manager
Centralized Visibility
- Monitor and manage all firewall policies from a single interface with SecureTrack.
- Quickly identify and address potential security threats across the network.
Consistent Policy Enforcement
- Ensure uniform application of security policies across multiple firewalls, reducing the risk of unauthorized access.
Automated Policy Updates
- Use SecureChange to automate routine policy updates, minimizing manual errors and freeing up time for critical tasks.
Compliance Officer
Centralized Visibility
- Monitor and manage all firewall policies from a single interface with SecureTrack.
- Quickly identify and address potential security threats across the network.
Consistent Policy Enforcement
- Ensure uniform application of security policies across multiple firewalls, reducing the risk of unauthorized access.
Automated Policy Updates
- Use SecureChange to automate routine policy updates, minimizing manual errors and freeing up time for critical tasks.
SOC Analyst
Centralized Visibility
- Monitor and manage all firewall policies from a single interface with SecureTrack.
- Quickly identify and address potential security threats across the network.
Consistent Policy Enforcement
- Ensure uniform application of security policies across multiple firewalls, reducing the risk of unauthorized access.
Automated Policy Updates
- Use SecureChange to automate routine policy updates, minimizing manual errors and freeing up time for critical tasks.
Network Architect
Centralized Visibility
- Monitor and manage all firewall policies from a single interface with SecureTrack.
- Quickly identify and address potential security threats across the network.
Consistent Policy Enforcement
- Ensure uniform application of security policies across multiple firewalls, reducing the risk of unauthorized access.
Automated Policy Updates
- Use SecureChange to automate routine policy updates, minimizing manual errors and freeing up time for critical tasks.
Cloud Security Engineer
Centralized Visibility
- Monitor and manage all firewall policies from a single interface with SecureTrack.
- Quickly identify and address potential security threats across the network.
Consistent Policy Enforcement
- Ensure uniform application of security policies across multiple firewalls, reducing the risk of unauthorized access.
Automated Policy Updates
- Use SecureChange to automate routine policy updates, minimizing manual errors and freeing up time for critical tasks.
CISO (Chief Information Security Officer)
Centralized Visibility
- Monitor and manage all firewall policies from a single interface with SecureTrack.
- Quickly identify and address potential security threats across the network.
Consistent Policy Enforcement
- Ensure uniform application of security policies across multiple firewalls, reducing the risk of unauthorized access.
Automated Policy Updates
- Use SecureChange to automate routine policy updates, minimizing manual errors and freeing up time for critical tasks.
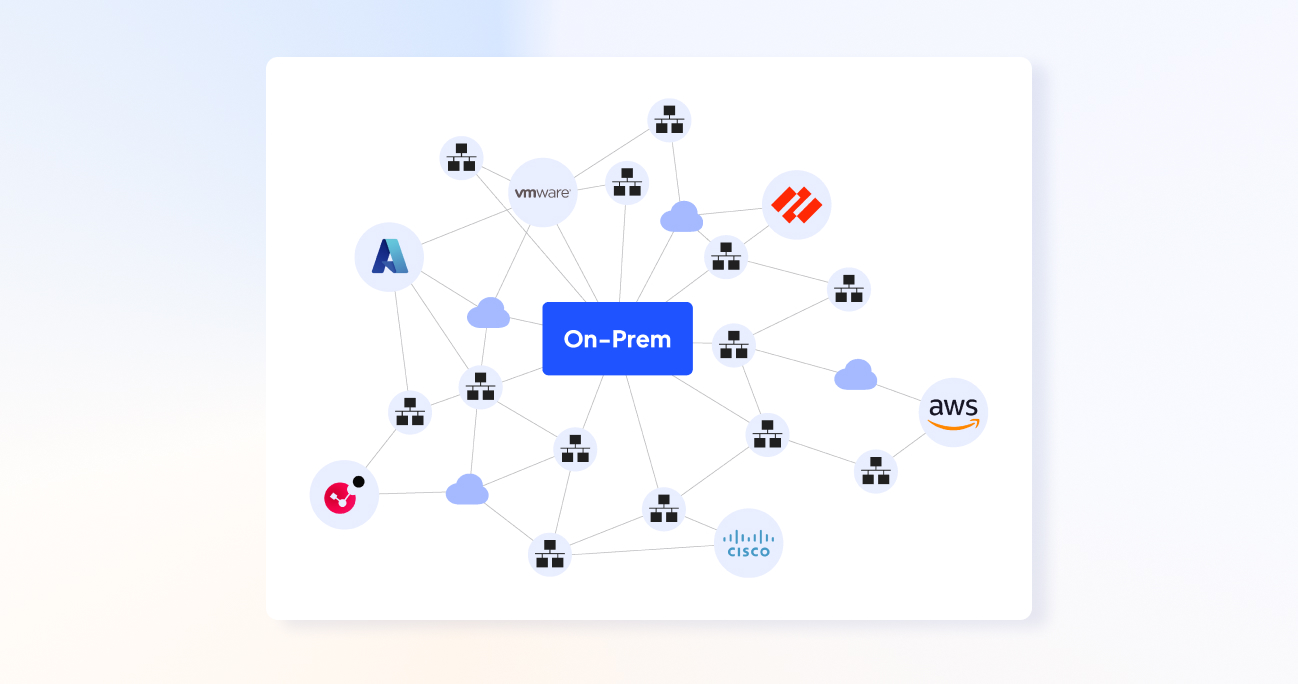
與您的日常工具無縫連接
Tufin 可以輕鬆地與您日常使用的工具和平台集成,簡化您的工作流程並增強您有效管理網路安全的能力。無論您是協調複雜的防火牆策略、確保合規性或管理多雲環境,Tufin 都能將您的所有系統整合在一起,提供統一、高效的體驗。
全面的多供應商支持
Tufin 可讓您通過直覺的介面管理所有主要供應商的防火牆策略,確保一致的實施並降低處理不同網路基礎架構的複雜性。
無縫合規集成
將 Tufin 與您現有的合規工具集成,以自動化審核流程、持續遵守行業法規,並減少合規管理所需的手動工作。
統一雲端平台連接
將 Tufin 的安全功能擴展到您的雲端環境,與 AWS、Azure、Google Cloud 等集成,以確保透過集中控制台在所有平台上一致地應用安全性原則。
整合安全資訊與事件管理 (SIEM)
將 Tufin 與 SIEM 工具結合,以整合安全數據,透過網路安全態勢的統一視圖,對安全事件做出更快、更明智的回應。
Firewall
Cloud
取得 Tufin,看得更清楚。
安排您的個人化簡報