Tufin recently released the latest update to Tufin Orchestration Suite. R16-4 has many new features. Today we’re going to take a closer look at the cloud tag policy feature.
It’s no secret that more and more organizations are moving workloads to the cloud. While this was once thought to be done for cost reduction purposes, it is clear today that the primary driver is agility: being able to move fast and continuously deploy capabilities to enable business growth and customer satisfaction. However, one of the concerns with cloud migration is security. According to a recent study of information security professionals, 62 percent of respondents are concerned that unauthorized outsiders could access data stored on public cloud services. Using an automated approach to define and enforce a central cloud tag policy is an effective component of a strong cloud security strategy.
The automation of security policies based on cloud tags can ease complexity and human error while increasing visibility and control. Cloud tags are a critical part of managing cloud instances and ensuring that the environment is properly maintained. Tufin’s cloud tagging feature enables cloud security administrators and cloud architects to define, manage, and enforce a tag policy for workloads running in the cloud that will allow them to create and align best practices for ensuring compliance in cloud environments.
What are tags good for?
- Organize resources and distinguish between them
- Control proliferation of workloads (save costs)
- Simplify deployment (for example: a new resource using other resources)
- Billing
- Assign security and compliance levels
Use Tufin’s Unified Security Policy to define, control, and enforce tag policy for workloads running in the cloud and for instances as they are being spun-up.
Here is how to get started using Tufin’s cloud tag policy:
How to define your policy:
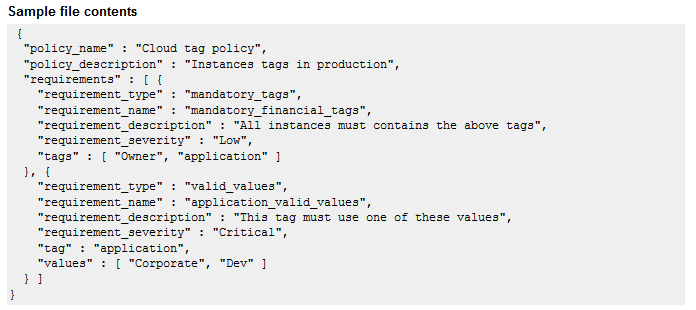
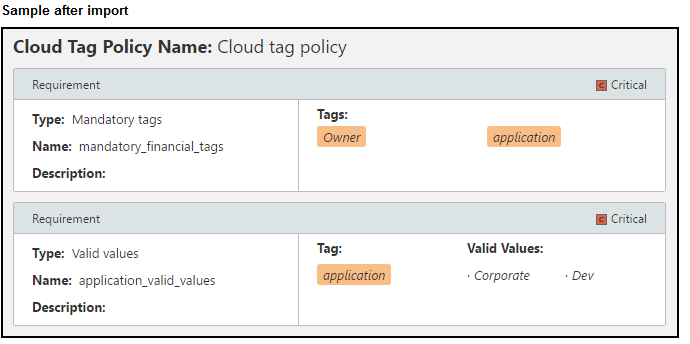
When you create a cloud tag policy file to import, you can include requirements for mandatory tags or valid values or both. You must include these fields:
- For mandatory tag requirements:
- policy name – The name of the cloud tag policy
- policy description – A description that is shown in the list of USP components
- requirement type – mandatory_tags
- requirement name – The name of the requirement in the cloud tag policy
- requirement description – A description that is shown in the list of cloud tag policy requirements
- requirement severity – A label that identifies that the requirement is either: Critical, High, Medium, Low
- tags – The tags that are required for every instance (case-sensitive)
- For valid values requirements:
- policy name – The name of the cloud tag policy
- policy description – A description that is shown in the list of USP components
- requirement type – Either mandatory_tags or valid_values
- requirement name – The name of the requirement in the cloud tag policy
- requirement description – A description that is shown in the list of cloud tag policy requirements
- requirement severity – A label that identifies that the requirement is either: Critical, High, Medium, Low
- tags – The tag that the values apply to
- values – The list of values that are valid for the tag
Ready to Learn More
Get a Demo